CCNA Discovery 4 Module 6 Exam Answers Version 4.0
1. A network engineer researched whether there are mechanisms available to help with the transition from an IPv4 addressing structure to IPv6. What three options did the engineer find?(Choose three.)
• A protocol translation mechanism allows communication between the IPv4 and IPv6 networks.
• A packet analyzer determines the addressing structure and converts it to the appropriate IPv4 or IPv6 scheme.
• New Core devices that support IPV6 must be purchased.
• A protocol converter changes IPv4 packets into IPv6 packets and vice versa.
• A dual-stack network design allows both IPv4 and IPv6 addressing to be used on all network devices.
• Tunneling allows IPv4 packets to be encapsulated so that they can traverse IPv6 networks and vice versa.
2. When should the command no auto-summary be used?
• with RIP version 1, to enable classless routing
• with RIP version 2, to enable classless routing
• with RIP version 1, when discontigous networks exist
• with RIP version 2, when discontigous networks exist
3. Refer to the exhibit. What must an administrator do on R3 to ensure that update packets are sent with subnet mask information?
• Add the commands:
R3(config-router)# auto-summary
R3(config-router)# no version 2
• Add the commands:
R3(config-router)# version 2
R3(config-router)# no auto-summary
• Change the network statement on R3:
R3(config)# network 10.10.4.0
• Add the command:
R3(config)# ip route 0.0.0.0 0.0.0.0 s0/0
4. What best describes a discontiguous network?
• combines several classfull networking address
• contains more than one route to a destination
• implements more than one routing protocol
• separated from the rest of the hierarchical group by another network
5. Refer to the exhibit. A company has decided to add a new workgroup. If the subnetting scheme for the network uses contiguous blocks of addresses, what subnet is assigned to WGROUP3?
• 172.16.3.12/29
• 172.16.3.16/29
• 172.16.3.20/29
• 172.16.3.24/29
• 172.16.3.32/29
6. A network administrator is using the 10.0.0.0/8 network for the company. The administrator must create a masking scheme to support 750 users at the main office and 620 users at the remote office. What mask should be assigned to the 10.0.0.0/8 network to preserve the most addresses?
• 255.255.255.0
• /19
• /20
• 255.255.252.0
• /23
• /21
7. What is another format for the IPv6 address 1080:0000:0000:0000:0000:0000:1267:01A2?
• 1080::1267:01A2
• 1080:0:0:0:0:1267:01A2
• 1080::0:1267:01A2
• 1080:::::1267.01A2
8. How many bits make up an IPv6 address?
• 32
• 48
• 64
• 128
9. After activating IPv6 traffic forwarding, configuring IPv6 addresses, and globally configure RIPng, what is the remaining step to activate RIPng?
• Enter the ipv6 router rip name command and then use network statements to activate RIPng on the interfaces.
• Enter the ipv6 router rip name command and then specify which interfaces run RIPng, which are passive, and which only receive.
• Enter the interface mode for each IPv6 interface and enable RIPng with the ipv6 rip name enable command.
• Enter the interface mode for each IPv6 interface and enable the multicast group FF02::9, and then activate RIPng globally using the ipv6 router rip name command.
• Enter the router rip command, and then activate RIPng using the version command.
• RIPng then automatically runs on all IPv6 interfaces.
10. Refer to the exhibit. The IT management has determined that the new subnet for WGROUP3 needs to be broken down into four more subnets. What would the subnet mask be for the four newly created subnets within WGROUP3?
• 255.255.128.0
• 255.255.192.0
• 255.255.224.0
• 255.255.248.0
• 255.255.252.0
11. Refer to the exhibit. What is the first usable IP address that can be assigned to the WGROUP3 switch?
• 172.16.50.96/27
• 172.16.50.97/27
• 172.16.50.98/27
• 172.16.50.99/27
• 255.255.255.0
12. Refer to the exhibit. Which set of router commands is required to turn on unequal-cost load sharing so that RTRA selects the path A-B-E and the lowest cost path A-C-E to the Internet?
• RTRA(config)# router eigrp 1
RTRA(config-router)# variance 2
• RTRA(config)# router eigrp 1
RTRA(config-router)# variance 1
• RTRA(config)# router eigrp 1
RTRA(config-router)# maximum-paths 2
• RTRA(config)# router eigrp 1
RTRA(config-router)# maximum-paths 1
13. Refer to the exhibit. Assuming that the default EIGRP configuration is running on both routers, which statement is true about Router A reaching the 2.2.2.0/24 network?
• The no auto-summary command needs to be issued to disable automatic summarization.
• The network 2.2.2.0 command needs to be issued to ensure that Router A recognizes the 2.2.2.0 network.
• EIGRP supports VLSM and automatically recognizes the 2.2.2.0 network.
• EIGRP does not support VLSM; therefore it cannot be used with discontiguous networks.
14. Refer to the exhibit. The network administrator wants router RTA to send only the summarized route of 10.10.0.0/16 to RTC. Which configuration accomplishes this?
• RTA(config)# interface s0/0
RTA(config-if)# ip summary-address eigrp 101 10.10.0.0 255.255.0.0
RTA(config-if)# exit
RTA(config)# router eigrp 101
RTA(config-router)# no auto-summary
• RTA(config)# interface s0/1
RTA(config-if)# ip summary-address eigrp 101 10.10.0.0 255.255.0.0
RTA(config-if)# exit
RTA(config)# router eigrp 101
RTA(config-router)# no auto-summary
• RTA(config)# interface s0/0
RTA(config-if)# ip summary-address eigrp 101 10.10.0.0 255.255.0.0
• RTA(config)# interface s0/1
RTA(config-if)# ip summary-address eigrp 101 10.10.0.0 255.255.0.0
15. What is a good design practice when developing a hierarchical addressing scheme?
• Address the nodes in the Access Layer and work toward the Core Layer.
• Assign addresses to the Core devices before planning the addressing scheme for the server farm.
• Determine where statically configured addressing will be implemented.
• Determine what percentage of devices are wired and what percentage of devices are wireless.
16. A network administrator is asked to design a new addressing scheme for a corporate network. Presently, there are 850 users at the head office, 220 users at sales, 425 at manufacturing, and 50 at the research site. Which statement defines the correct VLSM addressing map with minimal waste using the 172.17.0.0/16 network?
• 172.17.0.0/20 head office
172.17.1.0/21 manufacturing
172.17.1.0/22 sales
172.17.3.0/26 research
• 172.17.48.0/19 head office
172.17.16.0/20 manufacturing
172.17.48.128/25 sales
172.17.48.0/26 research
• 172.17.0.0/22 head office
172.17.4.0/23 manufacturing
172.17.5.0/24 sales
172.17.6.0/26 research
• 172.17.2.0/22 head office
172.17.3.0/23 manufacturing
172.17.4.0/26 sales
172.17.4.128/25 research
17. How would the routes for networks 172.16.1.0/24, 172.16.3.0/24, and 172.16.15.0/24 be summarized?
• 172.16.0.0/20
• 172.16.0.0/21
• 172.16.0.0/22
• 172.16.0.0/24
18. What two advantages does CIDR provide to a network? (Choose two.)
• dynamic address assignment
• automatic route redistribution
• reduced routing update traffic
• easier management of summarization
• automatic summarization at classfull boundaries
19. Which statement describes MD5 authentication for neighbor authentication?
• All passwords are sent in clear text when neighbors first learn about each other.
• Only the initiating router sends its password using encrypted text when it first discovers a new router.
• All routers send their password using encrypted text only when they first learn of each other.
• All routers send their password using encrypted text each time they exchange update packets.
20. Refer to the exhibit. What are the broadcast addresses for each subnet?
• Admin – 172.16.31.0
QA – 172.16.1.127
Development – 172.16.2.255
Sales – 172.16.32.255
• Admin – 172.16.31.255
QA – 172.16.1.255
Development – 172.16.3.255
Sales – 172.16.63.255
• Admin – 172.16.31.255
QA – 172.16.1.127
Development – 172.16.3.255
Sales – 172.16.63.255
• Admin – 172.16.31.0
QA – 172.16.1.255
Development – 172.16.2.255
Sales – 172.16.32.255
21. Refer to the exhibit. The IT management is adding three VLANs to the wgroup3 switch. The current subnet will be broken down to support 14 hosts for each of the new VLANs. What will the new subnet mask be for these VLANs?
• 255.255.255.192
• 255.255.255.240
• 255.255.248.0
• 255.255.255.224
• 255.255.240.0
• 255.255.255.248
22. An administrator is configuring IPv6 on a router. The steps that have already been completed are:
1. Activate IPv6 traffic forwarding.
2. Configure IPv6 addresses.
3. Globally configure RIPng.
What is the remaining step to complete the activation of RIPng?
• Enter the ipv6 router rip name command and then use network statements to activate RIPng on the interfaces.
• Enter the ipv6 router rip name command and then specify which interfaces run RIPng, which are passive, and which only receive.
• Enter the interface mode for each IPv6 interface and enable RIPng with the ipv6 rip name enable command.
• Enter the interface mode for each IPv6 interface and enable the multicast group FF02::9, and then activate RIPng globally using the ipv6 router rip name command.
• Enter the router rip command, and then activate RIPng using the version command. RIPng then automatically runs on all IPv6 interfaces.
23. Which range includes all available networks in the 192.168.8.0/21 network?
• 192.168.8.0/24 – 192.168.14.0/24
• 192.168.8.0/24 – 192.168.15.0/24
• 192.168.8.0/24 – 192.168.16.0/24
• 192.168.8.0/24 – 192.168.17.0/24
24. Which two are best practices for creating a new IP addressing scheme for a network? (Choose two.)
• Plan and allow for significant growth.
• Assign addresses to the access layer before any other layer.
• Plan the entire addressing scheme before assigning any addresses.
• Begin with the access layer network summary addresses and work to the edge.
• Plan the addressing scheme to meet the current minimum requirement needs.
• Implement statically assigned addresses to all hosts in the distribution layer first.
25. Refer to the exhibit. Which subnet will provide sufficient addresses for the Production network with minimal waste?
• 172.16.0.192/26
• 172.16.0.192/27
• 172.16.0.224/26
• 172.16.0.160/26
• 172.16.0.144/27
26. A network designer is implementing a new network for a company. The designer is using all new Cisco equipment and has decided to select a hierarchical routing protocol for the network. The designer wishes to minimize traffic from routing updates but also needs fast routing convergence in the event of a topology change. Also, the existing IP addressing scheme requires that the selected protocol support VLSM. Which routing protocol should be chosen?
• BGP
• RIP v1
• RIP v2
• OSPF
CCNA Discovery 4 Module 7 Exam Answers Version 4.0
1. A network engineer has decided to pilot test a portion of a new network design rather than rely on a prototype for proof-of-concept. What are two advantages of pilot testing a design concept?(Choose two.)
• The test network experiences real-world network traffic.
• Users within the enterprise are not affected by the test.
• Network response can be tested in unplanned and unpredictable situations.
• Unlikely failure conditions can be conveniently tested.
• Network response can be tested in a highly controlled simulated environment.
2. While preparing a network test plan document, a network designer records all initial and modified device configurations. Which section of the document typically contains this information?
• Appendix
• Test Procedures
• Test Description
• Actual Results and Conclusions
• Anticipated Results and Success Criteria
3. Refer to the exhibit. A network designer creates a test plan that includes the specification shown. In which section of the test plan would this specification be found?
• Test Description
• Test Procedures
• Design and Topology Diagram
• Actual Results and Conclusions
• Anticipated Results and Success Criteria
4. What OSI model Layer 2 security measure can a network engineer implement when prototyping network security?
• a firewall at the network edge
• port security at the access design layer
• port security at the distribution design layer
• IP access control lists at the access design layer
5. How do designers decide which network functions need to be included in the prototype test?
• They select the functions that align with the business goals.
• They select the functions that occur at the network core.
• They select the functions that do not exist in the existing network.
• They select the functions from a list of generic network operations.
6. Refer to the exhibit. During prototype testing of the Cisco network shown, connectivity must be verified. Assuming all connections are working and CDP is enabled on all devices and interfaces, on which device was the command issued?
• R1
• S1
• R3
• S2
• R5
• S3
7. Refer to the exhibit. During prototyping, Layer 2 functionality is being tested. Based on the output shown, which two pieces of information can be determined? (Choose two.)
• Switch1 is the root bridge.
• Interface Fa0/2 on Switch1 has no role in the operation of spanning tree.
• Interface Fa0/2 on Switch1 is the alternate port used to reach the root bridge.
• Based on the entries in the “Role” column, it can be concluded that RSTP has been implemented.
• Interface Fa0/1 on Switch1 is the forwarding port selected for the entire spanning-tree topology.
8. What Rapid Spanning Tree Protocol (RSTP) state is given to the forwarding port elected for every switched Ethernet LAN segment?
• root
• backup
• alternate
• designated
9. Refer to the exhibit. During prototype testing, verification of VLAN connectivity is being performed. Based on the information shown, what command produced the output?
• show spanning-tree
• show interfaces trunk
• show cdp neighbors
• show interfaces
• show ip interface brief
10. Switch port Fa0/24 was previously configured as a trunk, but now it is to be used to connect a host to the network. How should the network administrator reconfigure switch port Fa0/24?
• Use the switchport mode access command from interface configuration mode.
• Enter the switchport nonegotiate command from interface configuration mode.
• Administratively shut down and re-enable the interface to return it to the default.
• Enter the no switchport mode trunk command in interface configuration mode.
• Use the switchport access vlan vlan number command from interface configuration mode
• to remove the port from the trunk and add it to a specific VLAN.
11. Refer to the exhibit. The redundant paths are of equal bandwidth and EIGRP is the routing protocol in use. Which statement describes the data flow from Server to PC2?
• EIGRP load balances across the R3 to R1 and R3 to R2 links.
• EIGRP load balances across the R1 to Switch3 and R2 to Switch3 paths.
• EIGRP load balances across the Switch1 to Switch3 and Switch1 to Switch2 paths.
• EIGRP does not load balance in this topology.
12. A network designer needs to determine if a proposed IP addressing scheme allows efficient route summarization and provides the appropriate amount of scalability to a design. What is useful for validating a proposed hierarchical IP addressing scheme?
• NBAR
• a pilot network
• a route summary
• a network simulator
• a physical topology ma
13. In the router command encapsulation dot1q 10, what does the number 10 represent?
• the metric used for a particular route
• the number of the VLAN associated with the encapsulated subinterface
• the priority number given to the device for the election process
• the number that must match the Fast Ethernet subinterface number
• the number used to program the router for unequal cost path load balancing
14. Refer to the exhibit. The users on the 192.168.10.192 network are not allowed Internet access. The network design calls for an extended ACL to be developed and tested. Where should the ACL be placed for the least effect on other network traffic?
• inbound on Fa0/0 of R3
• outbound on Fa0/0 of R3
• inbound on Fa0/1 of R3
• outbound on Fa0/1 of R3
• inbound on Fa0/1 of R2
• outbound on S0/0 of R2
15. Refer to the exhibit. What two measures can be taken to address the areas of weakness circled in the network design? (Choose two.)
• Provide redundant connections to all end users.
• Add another core switch to increase redundancy.
• Add a switch in the server block connecting the server farm to each core switch.
• Add an additional switch to the DMZ and direct links from the new switch to the core switches.
• Provide a redundant firewall router connecting to a second ISP, the core switches, and the DMZ.
16. Why is it important to record baseline measurements of a prototype network?
• Test results show security weaknesses after the baseline tests are run.
• The baseline is the point at which the network is operating at its fullest potential.
• Baseline measurements define a point at which network traffic has exceeded the designed capabilities of the network.
• Test results are compared to the baseline to see how the test conditions increase processor use or decrease available bandwidth.
17. Refer to the exhibit. A network administrator has been given the task of creating a design for a temporary classroom building that is to be set up outside an overcrowded school. In testing the prototype, it is found that the student PC cannot ping the teacher PC. All the switch interfaces are active and connected properly, as is interface Fa0/0 of the router. Given that only the commands shown have bee added to the router configuration, what is the source of the problem?
• The IP settings on the student PC are incorrect.
• The default gateway on the teacher PC is misconfigured.
• The router Fa0/0 interface has not been configured as a VLAN trunk.
• The Fa0/0 physical interface has not been configured with an IP address and subnet mask.
• The administrator forgot to configure a routing protocol to allow the ping packets to reach the teacher PC subnet.
18. Refer to the exhibit. Why are interfaces Fa0/11, Fa0/23, and Fa0/24 not shown in this switch output?
• Interfaces Fa0/11, Fa0/23, and Fa0/24 are trunks.
• Interfaces Fa0/11, Fa0/23, and Fa0/24 are shutdown.
• Interfaces Fa0/11, Fa0/23, and Fa0/24 are blocking.
• Interfaces Fa0/11, Fa0/23, and Fa0/24 failed diagnostics
19. Refer to the exhibit. A network technician is performing an initial installation of a new switch in the east wing. The technician removes the switch from the box, makes the connections to the network, and adds the configuration shown. The technician notifies the network administrator that the switch has been installed. When the network administrator at the home office attempts to telnet to the switch from host 192.168.0.1, the connection fails. What action should the network technician take?
• Add an enable password to the switch.
• Add a default gateway to the switch configuration.
• Configure the switch with an IP access list to permit the host connection.
• Enable the physical interfaces of the switch with the no shutdown command.
20. Refer to the exhibit. After all the interfaces have stabilized, what is the spanning-tree state of all the enabled interfaces of SW11?
• discarding
• forwarding
• learning
• listening
1. Which mechanism is used to create a floating static route?
• administrative distance
• cost
• hop count
• passive interface
2. IPSec operates at which layer of the OSI model?
• application
• network
• datalink
• transport
3. Which is true regarding Frame Relay LMI?
• There are three LMI types standardized by ANSI, ITU-T, and Cisco.
• Routers at each end of a Frame Relay virtual circuit must always use the same LMI type.
• The LMI type must be manually configured.
• The only function of LMI is to verify the connection between the router and the Frame Relay switch.
4. Which statement identifies the IP address design for subinterfaces that are configured for a Frame Relay network?
• Multipoint configurations require the IP address of each subinterface on each router to be in its own subnet.
• Multipoint configurations require IP addresses for each subinterface on each router to be a part of the same subnet.
• Point-to-point configurations require IP addresses for each subinterface on each router to be a part of the same subnet.
• Point-to-point configurations do not require IP addresses on each subinterface on each router.
• Multipoint configurations do not require IP addresses on each subinterface on each router.
5. Which three algorithms can be used to encrypt user data in an IPSec VPN framework? (Choose three.)
• 3DES
• AES
• Diffie-Hellman
• DES
• ESP
• SHA
6. Which flag is set by a Frame Relay switch to inform the receiving station that congestion was experienced?
• BECN
• DE
• FECN
• FCS
7. Refer to the exhibit. The complete configuration of a Frame Relay interface on the Chicago router is shown. How does the Chicago router know which DLCI is mapped to the IP address of the remote router?
• DE
• CIR
• FECN
• Inverse ARP
8. What statement correctly defines the purpose of the split horizon rule?
• marks the route unreachable in a routing update that is sent to other routers
• prevents routers from advertising a network through the interface from which the update came
• prevents routers from accepting higher cost routes to networks previously marked as inaccessible before the timer expires
• limits the number of hops a packet can traverse through the network before it should be discarded
9. Which PVC status suggests that the router recognizes the DLCI configured on its interface as being present on the Frame Relay switch, but the PVC associated with the DLCI is not capable of end-to-end communication?
• active
• deleted
• inactive
• idle
10. Refer to the exhibit. Which router command is used to associate a Layer 2 address with the corresponding Layer 3 address?
• Miller(config-if)#frame-relay map ip 172.16.150.1 110
• Miller(config-if)#frame-relay map ip 172.16.150.1 112
• Miller(config-if)#frame-relay map ip 172.16.150.2 110
• Miller(config-if)#frame-relay map ip 172.16.150.2 112
11. A network administrator issued the command show frame-relay pvc. The response from the router shows the status of a PVC as deleted. What is the reason for this status?
• The DLCI is using the wrong LMI type.
• The DLCI is usable but has little activity.
• The DLCI is programmed in the switch but the circuit is not usable.
• The DLCI configured on the CPE device does not match the DLCI.
12. What is one benefit of using a network simulation software package?
• The network design can be tested before it is actually implemented.
• Simulation software packages are quickly updated to support new network technologies and devices.
• Simulated devices have the same features as actual devices, allowing for detection of all potential problems.
• Software packages can simulate all possible network traffic conditions, giving an accurate prediction of network performance.
13. What are two components a network designer considers when planning a VPN? (Choose two.)
• encryption algorithm for privacy and security
• encapsulation protocol to use when creating the VPN tunnel
• switching technology to optimize VPN WAN throughput
• tunneling technology for guarding against data corruption
• routing protocol on the gateway for optimum performance
14. When identifying VPN requirements for endpoint users, what care must be taken to protect the network when remote users log in from unsecured public locations?
• Ensure that the user has VPN client software that allows access to all internal resources.
• Ensure that the VPN user traffic does not slow down internally sourced traffic on the network.
• Ensure that there are no obstacles to hamper the users from accessing all internal resources.
• Ensure that remote users can only access network resources that are appropriate to their job function.
15. Which two components are key elements when implementing a VPN? (Choose two.)
• concentration
• encryption
• prioritization
• compression
• encapsulation
16. What tool can help ease the configuration of VPN servers on routers?
• Cisco SDM
• PIX Firewall
• Cisco VPN Concentrator
• Cisco Adaptive Security Appliances
17. What is used to identify the path to the next frame-relay switch in a Frame Relay network?
• CIR
• DLCI
• FECN
• BECN
18. Which two statements are true regarding VPN security? (Choose two.)
• Users may only establish a VPN connection from secure locations and never from public areas.
• Users that connect to a network through a VPN do not have to log in to resources on the network.
• Users that connect to a network through a VPN are are considered trusted users on the network.
• Users may establish a VPN connection from unsecure locations such as airports and hotel lobbies.
• Users that connect to a network through a VPN should have access to all the resources on the network.
19. Refer to the exhibit. What is placed in the address field of a frame that will travel from the Orlando office to the DC office?
• MAC address of the Orlando router
• MAC address of the DC router
• 192.168.1.25
• 192.168.1.26
• DLCI 100
• DLCI 200
20. Two directly connected routers are able to ping each other through the Serial 0/0/0 interfaces. A network administrator changes the encapsulation on one router to PPP, and the other is left at the default value. What statement would appear in the output of the show interfaces command issued on one of the routers?
• Serial 0/0/0 is up, line protocol is up
• Serial 0/0/0 is down, line protocol is down
• Serial 0/0/0 is up, line protocol is down
• Serial 0/0/0 is down, line protocol is up
• Serial 0/0/0 is administratively down, line protocol is down
21. Refer to the exhibit. What statement is true about the configuration shown for R2?
• R2 is configured as the Frame Relay switch.
• R2 is configured as the main site in a multipoint Frame Relay WAN prototype.
• R2 is configured as the main site in a point-to-point Frame Relay WAN prototype.
• R2 is configured as a remote site in a multipoint Frame Relay WAN prototype.
• R2 is configured as a remote site in a point-to-point Frame Relay WAN prototype.
22. A company uses serial interfaces on its border router to connect to branch offices through WAN connections. The security policy dictates that the encapsulation should use PPP with authentication protocol CHAP. Which statement is true about the configuration requirement of CHAP?
• Both the username and password are case sensitive.
• Neither the username nor the password is case sensitive.
• The username is case sensitive but the password is not case sensitive.
• The password is case sensitive but the username is not case sensitive.
23. Which two statements about split tunnels are true? (Choose two.)
• Local LAN printing will use the VPN tunnel.
• The traffic load on the VPN server is increased.
• Traffic to the corporate network will be encrypted.
• There is a reduced security risk to the corporate network.
• All traffic travels across the VPN tunnel from client to server.
• Traffic to public web sites and general Internet navigation is not encrypted.
24. An IP address has been assigned to the S0/0/0 interface of a new Cisco router. The administrator wishes to quickly test basic connectivity with the serial interface of an adjoining Cisco router via the use of the default WAN protocol. Which WAN protocol will be used for this test?
• PPP
• Frame Relay
• DSL
• HDLC
• ATM
25. Which two statements about split tunnels are true? (Choose two.)
• Local LAN printing will use the VPN tunnel.
• The traffic load on the VPN server is increased.
• Traffic to the corporate network will be encrypted.
• There is a reduced security risk to the corporate network.
• All traffic travels across the VPN tunnel from client to server.
• Traffic to public web sites and general Internet navigation is not encrypted.
CCNA Discovery 4 Module 9 Exam Answers Version 4.0
1. Which two statements describe factors that influence the layout of a proposal? (Choose two.)
• Proposal layouts are required to use sans serif typefaces.
• A specific proposal layout is followed when one is specified in the RFP.
• A designer chooses the layout if a written RFP does not specify an outline.
• The software that is used to create the proposal dictates the proposal layouts.
• Proposal layouts are required to use a format that is designed by the network engineer.
2. What two items are typically included in the executive summary of a proposal? (Choose two.)
• project scope summary
• high-level implementation plan
• quotes for all needed equipment
• technical requirements for the design
• emphasis on the benefits that meet the goals of the customer
3. Which proposal section describes the intended routing protocol, security mechanisms, and addressing for the planned network?
• logical design
• physical design
• executive summary
• implementation plan
• network requirements
4. Which occurrence would indicate a failure of the design phase?
• The incorrect model switches were ordered.
• There is no customer signoff for task completion.
• New requirements are identified after implementation begins.
• The new network capacity is inadequate to support required traffic.
5. A network installation team is assigned to replace all core switches in an existing data center. No other upgrades are planned. Which kind of installation is this?
• a new installation
• a fork-lift installation
• a phased installation
• a green field installation
6. What service is provided Cisco standard warranty?
• software application maintenance
• replacement of defected hardware
• next business day delivery of replacement parts
• access to the Cisco Technical Assistance Center (TAC) 24 hours a day, 7 days a week
7. An upgraded version of the Cisco IOS has been purchased. However, the CD arrived damaged. How will this loss be covered?
• a hardware warranty
• a software warranty
• the Cisco SMARTnet Service
• an additional service contract
8. A company informs the account manager that the installation of a new edge router at the customer remote branch location cannot be done at the scheduled time because of a large order that the branch office needs to complete. As a result, the end date of the project must be adjusted to accommodate the additional time. What is the action should the account manager take?
• Cancel the order for the new edge router.
• Work with designer to redesign the branch network.
• Instruct the technician to complete the install of the router at on the date in the contract.
• Adjust the timeline documentation to show the company how the delay will affect the
• project completion date.
9. NetworkingCompany completes the installation of a network upgrade for a retail customer. All of the onsite tests complete successfully and the customer IT staff approves the results of the tests. The manager of the retail store contacts NetworkingCompany to inform the company that the store will not pay for the upgrade until a recently purchased software package is installed and tested on the network. Which two items that are contained in the proposal can the account manager refer to when discussing this issue with the store manager?(Choose two.)
• the project scope
• the bill-of-material
• the project timeline
• the terms and conditions
• the business goals of the customer
• the evaluation of the current network
10. The operation of a new branch location network is delayed because a VPN cannot be configured and established between the branch location and the main office. It is determined that the router at the main office does not have enough memory and does not have the correct Cisco IOS version image to support the VPN features. To prevent this delay, this problem should have been identified and corrected during which part of the design project?
• the preparation of the business case
• the prioritizing of the technical goals
• the characterization of the existing network
• the implementation of the approved design
11. The NetworkingCompany team is tasked to prepare an implementation schedule for a customer. It is determined that the new firewalls and wireless controllers that are specified in the design cannot be delivered and installed within the agreed upon time frame. The NetworkingCompany informs the customer of the problem. What two options can the NetworkingCompany team take to ensure the success of the project? (Choose two.)
• plan to add additional staff and resources to shorten the installation time after the new equipment is delivered
• eliminate redundancy in the design to reduce the amount of equipment that is needed
• renegotiate a new time frame with the customer to accommodate the delay
• delay the installation of the security devices and controllers until a later time
• redesign the network to use only readily available equipment and software
12. AAA Financial Services Company is performing implementation planning for a core switch upgrade. The company has 200 financial software programmers that work billable hours during the week. They have critical, scheduled money transfer transmissions that occur at hourly intervals every night. There are two, two-hour long IT maintenance windows scheduled for software upgrades, one on Saturday and one on Sunday. The bank advertises online banking as available 24 hours on business days and 21 hours on the weekends. However, a network upgrade that is necessary to replace some switches is expected to take four hours. Because of rack constraints, this time includes three hours to remove the old switches before the new switches can be installed and one hour to test the logical configuration. How should the implementation scheduling be handled
• Defer the software upgrades. Use the Saturday window to perform the hardware installation. Use the Sunday window to perform the logical testing.
• Coordinate and publish a separate four-hour downtime during Friday to perform the complete switch installation and testing process. Use the Saturday and Sunday windows to correct any outage problems after the Friday window.
• Coordinate and publish two, four-hour downtimes incorporating the published Saturday and Sunday windows. Defer any software upgrades until the new network is proven to be working
correctly with the old software. Use the Sunday window as a fallback scheduling period if there re problems necessitating backing out of the Saturday window.
• Coordinate and publish an eight-hour downtime incorporating the Saturday window. This ill allow four hours for installation and logical testing, one hour for troubleshooting and decision, and three hours to roll back to the previous configuration if the new switching cannot pass the logical testing. Defer any software upgrades until the new network is proven to be working orrectly with the old software.
13. ncluded in a Bill of Materials (BOM) for a SOHO wired implementation is a Cisco 2811 router, Catalyst 2560 switch, four PCs, three laptops, and a networked printer. Wireless LAN capability will be implemented on this network. Which two equipment types must be added to the BOM to implement this request? (Choose two.)
• DNS server
• LAN switch
• wireless NICs
• DHCP server
• wireless access points
14. A customer has just taken delivery of a Cisco 2811 router and Catalyst 3560 switch. Included with the purchase is the SMARTnet Service. Which two resources are included with SMARTnet Service? (Choose two.)
• signature file updates
• technical support from TAC
• maintenance releases for OS
• software application major releases
• software application maintenance and minor releases
15. A Cisco 1841 router has been purchased without an agreement for SMARTnet Service. What two items are guaranteed under the standard warranty? (Choose two.)
• access to TAC
• replacement of defective physical media
• advanced replacement of hardware parts
• access to a renewable standard warranty contract
• under normal use, replacement of defective hardware
16. Upon completion of a proposal, a network design team must sell their ideas to two key stakeholders. Who are these two stakeholders? (Choose two.)
• customers
• licensing boards
• cabling contractors
• internal management
• project implementation team
17. What are two important guidelines when creating a slide presentation for a meeting with a customer? (Choose two.)
• Use all capital letters on words and phrases when possible for added emphasis.
• Provide varied background graphics to enhance viewer interest.
• Use contrasting colors for background and text to aid visibility.
• Change fonts frequently to denote differences in subject matter.
• Use bulleted text to lead the discussion.
18. In order to finalize a project proposal, an account manager of a
• networking company creates the terms and conditions section. What are two clauses that should be included in this section? (Choose two.)
• cost summary
• installation steps
• change order procedures
• problem resolution process
• maintenance contract quotation
19. Which two items will a systems engineer include in an implementation plan? (Choose two.)
• references to design documents
• the business goals of the customer
• diagrams of the existing traffic flows
• the steps to install and test the network
• cost of each network device and component
20. Which statement describes a phased installation into an existing network?
• A phased installation generally takes less time and expense than a green-field installation.
• A phased installation is not suitable for large, multi-site network installations or upgrades.
• A phased installation requires detailed planning in order to avoid disruption of user services.
• A phased installation involves building an entire replacement network and migrating users over to it.



















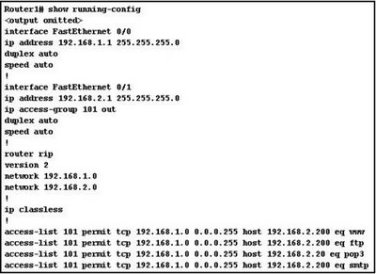 efer to the exhibit. Host 192.168.1.14 is unable to download email from 192.168.2.200. After reviewing the output of the show running-config command, what problem is discovered?
efer to the exhibit. Host 192.168.1.14 is unable to download email from 192.168.2.200. After reviewing the output of the show running-config command, what problem is discovered?











